The Global Eye
What business challenge can we help you solve?
Managed Security Services Provider - MSSP
Global IT Managed Security Services Provider (MSSP)
As part of our MSSP offering, Global IT provides helpdesk support and technology due diligence to maintain and improve existing IT environments. In light of today’s evolving threat landscape, we also offer a specialized cybersecurity team focused on protecting your organization’s digital assets.
Our certified cybersecurity professionals work closely with the MSP team to proactively identify and resolve security issues, implement system improvements, and mitigate vulnerabilities.
Our Managed Security Services include:
- Email, Systems, and Network Hardening
- User testing and training
- Privileged Access Management (PAM) audits
- Multi-factor authentication (MFA) integration
- End-of-Life (EoL) systems oversight
- Information Security Management Plan (ISMP) development
- Incident Response Plan (IRP) creation
- Backup and disaster recovery planning
- Business Continuity Planning (BCP)
- Monthly device inventory compliance audit scanning and reporting (Sonar Class 4)
All identified vulnerabilities are logged, reported, and addressed in coordination with the MSP team to ensure timely remediation and sustained protection.
For organizations that require compliance management and reporting, we recommend the MSSP Security Plus plan as a minimum. The Global IT Security Plus MSSP plan includes Global Eye–Sonar Class 4 compliance monitoring and reporting.
Global IT Security Essentials
- Network hardening – protects your business from the outside with real-time threat intelligence and comprehensive network controls.
- Systems hardening – Ensures your systems are compliant by eliminating risky configurations and services.
- Regular updates & patching – Zero-day and vulnerability notification and remediation guidance.
- Identity and Access Management—IAM is configured to ensure that only authorized people have access to your systems and data.
- Security User Awareness Program – Keep your users security savvy with security-based user awareness training.
- Engage annually with 3rd party insurance renewal documentation (written only)
Global IT Security Plus
- Includes all the components from the essentials plan and in addition
- Network hardening – protects your business from the outside with real-time threat intelligence and comprehensive network controls.
- Systems hardening – Ensures your systems are secure and compliant by eliminating risky configurations and services.
- Regular updates & patching – Zero-day and vulnerability notification and remediation guidance.
- Monthly vulnerability, threat, and attack surface reports – Know which systems and networks are vulnerable, and provide specific information on the type of threats your organization faces.
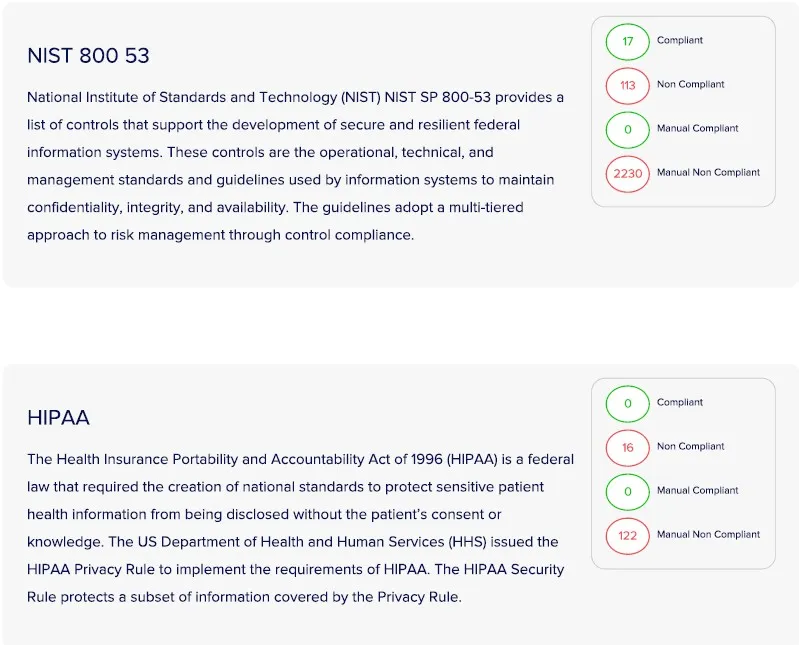
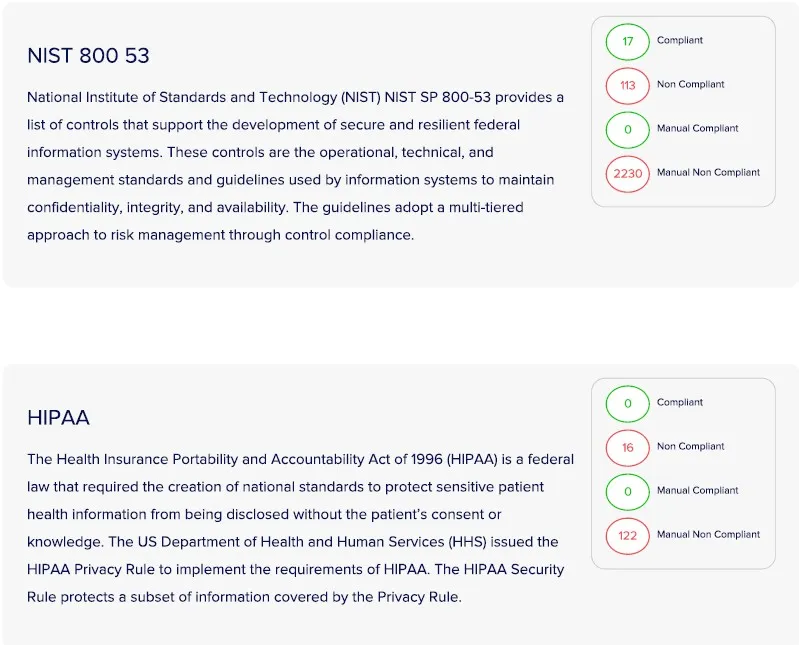
- Compliance Readiness Review: Know where you stand with your sensitive data. Compliance frameworks include CCPA, PCI-DSS, and HIPPA.
- Identity and Access Management—IAM is configured to ensure that only authorized people have access to your systems and data.
- Email Security – Email hardening and security. Includes tailored phishing campaigns and reports on user awareness.
- Security User Awareness Program – Keep your users security savvy with security-based user awareness and training.
- Engage annually with 3rd party insurance renewal documentation and 3rd party audit support with control evidence and documentation.
Global IT Vanguard Security
- Includes all the components from the Essentials and Plus MSSP plans, with the following added services and benefits:
- Network hardening – protects your business from outside IT with real-time threat intelligence and comprehensive network controls.
- Network Monitoring—Seconds count. Real-time network threat monitoring helps identify threat trends and usage and supports incident response.
- Annual Network Penetration Testing—Once annually, external or internal network penetration testing, also known as Pen testing, shines a light on your network and validates the controls in place.
- On-site Security Review – Most organizations fail to realize the value of physical security. Whether a data center or office location, physical security
- Systems hardening – Ensures your systems are secure and compliant by eliminating risky configurations and services.
- Regular updates & patching – Zero-day and vulnerability notification and remediation guidance.
- Endpoint Detection and response (EDR): Protect your Endpoints with a local firewall, antimalware, and file integrity monitoring. Keep your endpoints safe with customized EDR.
- Monthly vulnerability, threat, and attack surface reports – Know which systems and networks are vulnerable and specific information on the type of threats your organization faces.
- Compliance Readiness Review: Know where you stand with your sensitive data. Compliance frameworks include CCPA, PCI-DSS, and HIPPA.
- Identity and Access Management—IAM is configured to ensure that only authorized people have access to your systems and data.
- Email Security – Email hardening and security. Includes tailored phishing campaigns and reports on user awareness.
- Security User Awareness Program – Keep your users security savvy with security-based user awareness and security training.
- Engage annually with 3rd party insurance and security audits.
Additional Services
- Compliance Readiness for PCI-DSS, HIPPA, CCPA
- Internal Network and Systems Review
- Internal and External Penetration Testing
- Comprehensive Cyber Security Policy Creation
Why Choose the Global Eye Security Monitoring System?
Free protection can be unreliable, ineffective, and preinstalled with spyware. Data loss, outage time, ransomware, or damaged reputation can cost your business thousands of dollars. Investing in reliable data security systems is a great way to protect your brand and business operations.
One of our customers (5-star hotel in Beverly Hills) decided to make the switch to Global IT. They already had a security system, but we recommended they switch. Immediately, Global Eye picked up malware and security vulnerabilities that their old vendor and software didn’t detect. Global IT quickly took control of the malware and removed it, never to return again.
With vast experience, Global IT Eye can detect vulnerabilities that our competitors cannot.
Security systems are great but only fully effective with a well-orchestrated, managed service provider plan.
- Flow record with blacklist monitoring
- Penetration testing
- Policy enforcement
- Remote and on-site support
- Onsite preventative maintenance and support
- Monitor network health and performance
- Track and work with 3rd party vendors
- Long and short-term planning
- Hardware/software sourcing
- Telecom Services Monitoring
Managed services packages can be customized for every business demand.
Global IT has 100% 5-star reviews on Yelp and was ranked one of the 30 Best Small Companies to Watch by the Silicon Review. Shop our managed IT packages today.
Sonar Class 1 is our powerful Enterprise EDR/XDR-based application tool, expertly designed to uncover anomalous behavior and breaches, conduct risk assessments, respond effectively to incidents, carry out thorough investigations, and ensure robust remediation. With its enterprise license, it is seamlessly integrated into any device, enhancing visibility, optimizing risk management, and strengthening your response against threats posed by APT (Advanced Persistent Threats). Sonar Class 1 sends its event data to our logging server, which is diligently monitored daily by a skilled administrator.
- Precisely detect advanced persistent threats
- Effectively stop fileless attacks
- Proactively block zero-day threats
- Shield your organization against ransomware
- Prevent violations of company policy
- Streamline log management
Increased visibility:
Gain early insights into covert insider threats, phishing attempts, or other attacks that typically target enterprises
Improved risk management:
Enterprise Inspector processes vast amounts of data in real-time, minimizing response times, addressing security issues promptly, and enhancing overall security posture
Response to Advanced Persistent Threats (APT):
Ideal for threat hunting, ESET Enterprise Inspector provides proactive measures to prevent future attacks, including subtle APTs.
Automation for the mitigation of:
- Emerging forms of ransomware
- Your business is equipped with advanced tools to proactively detect ransomware and receive timely alerts if ransomware-like behavior is identified on the network.
- Behavior detection and repeat offenders
- On your network, specific users are persistent malware offenders. These individuals continue to fall victim repeatedly.
- Threat hunting and blocking
- An alert for a new threat has reached your early warning system or security operations center (SOC). What actions will you take next?
In conjunction with the Global IT MSP and MSSP plans, Global IT is dedicated to actively engaging with events, opening tickets to meticulously track and log occurrences that raise concerns that could impact security, productivity, and performance.
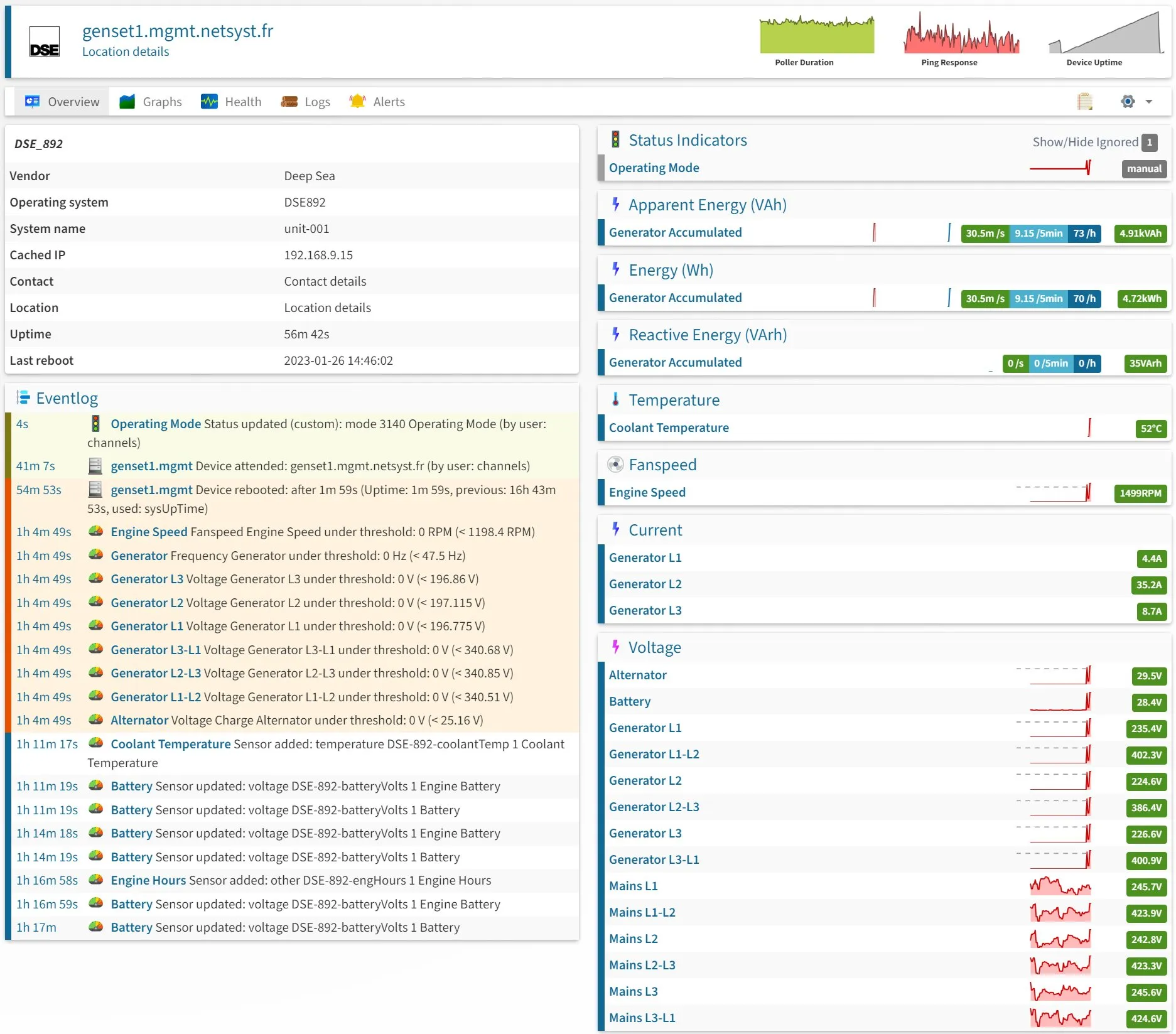
Sonar Class 2 is our server based application that is used for server specific resource events, resource alerts, monitoring and logging of anything related to a server where this is installed on. Sonar Class 2 is a license that can be added to any device and reports data back to our logging server that is monitored daily by an administrator.
- Network: Incoming and outgoing traffic, bandwidth usage, packet loss, interface error rates, TCP connections, link status, and interface speed
- Servers: Load on processors, network cards, and memory, amount of space on hard drives, and temperature of components
- Websites: Validity of SSL certificates
- Applications: Correct execution of SQL queries
Along with the Global IT MSP and MSSP plans, Global IT will proactively open tickets, logging events that arise concern that could cause any potential performance issues. Issues such as resource limitations, unusual resource activities, spikes in load, and everything that can help us understand what specifically is happening on the device this agent is installed on.

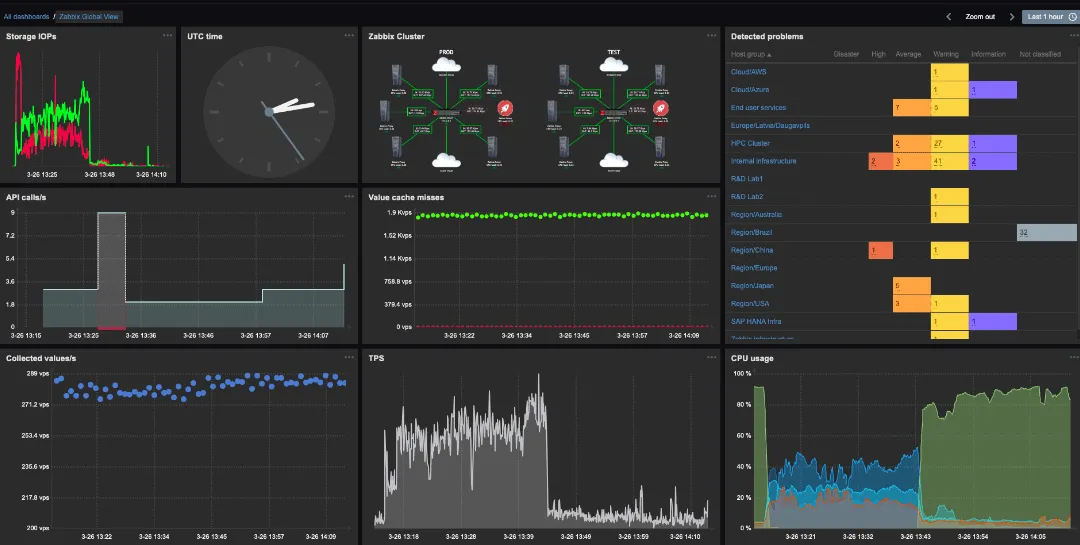
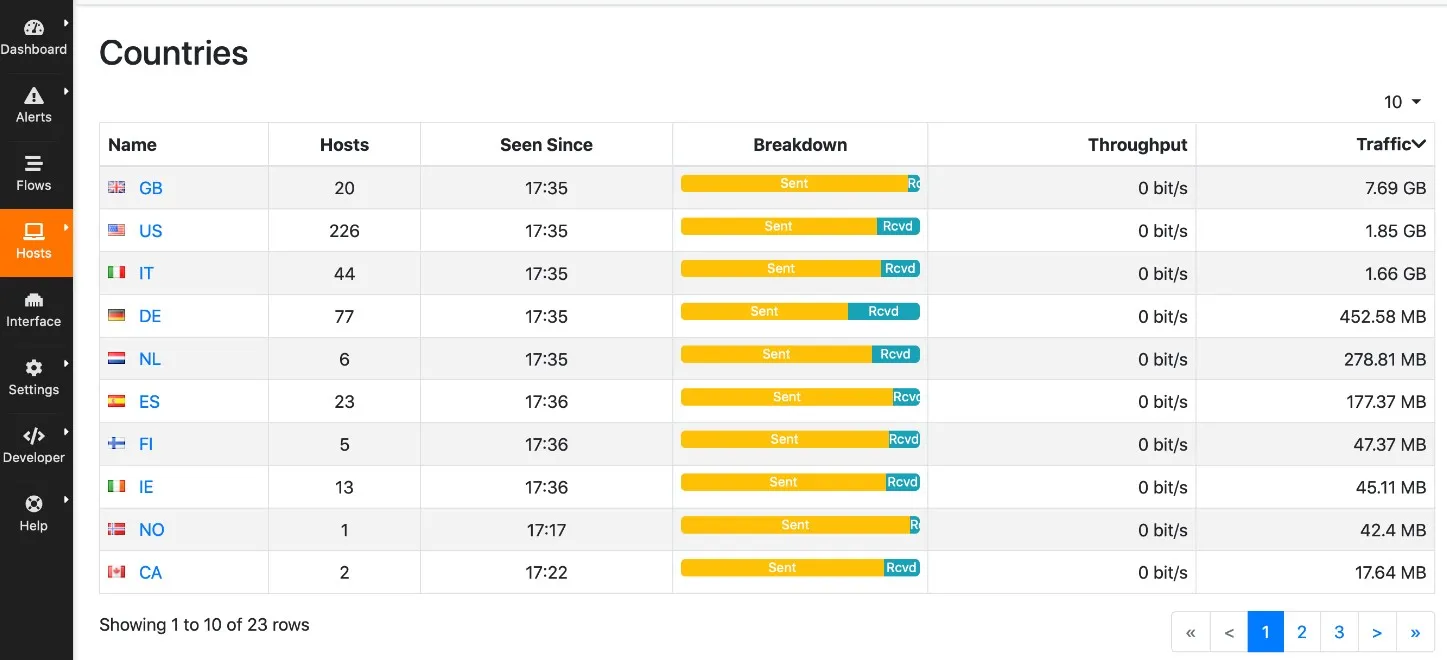
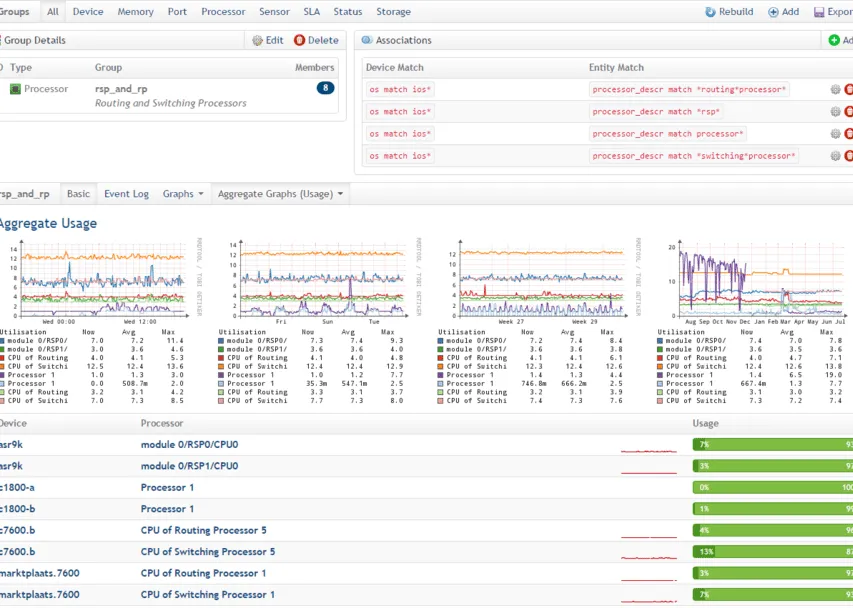
Sonar Class 3 is included with our premium and enterprise MSSP Managed Security Service Provider plans.
Sonar Class 3 includes constantly scanning the network for newly added devices, rouge devices, recording and logging every single IP connection from outside in and inside out, for everything that passes through the internet interface we have configured. The logs are then retained and queried for alerts, unusual activities, etc.
- Traffic in/out logging and reporting what type of traffic, etc.
- IP lookup and policy association (good, alert, bad)
- Monitoring network performance, detecting spikes, analyzing behaviors, detecting drops, traffic distribution, trends, etc.
- Monitor network activity with hosts and flows, and uncover suspicious or unwanted network activities.
- Logging all network devices, and recording logins, configuration changes, etc.
Sonar Class 3 is a very powerful tool in the right hands and is ideal for large organizations and network engineers looking for visibility into network traffic. Sonar Class 3 empowers Global IT MSSP teams with the ability to view active traffic, and provide immediate action and responses to potential threat actors.
Sonar Class 4 is a licensed vulnerability and compliance management platform that automates measuring and reporting under careful the direction from the technical team. The licensed tool scans client devices for the latest threats, it identifies security vulnerabilities and associates the risk against compliance frameworks and provides automated reporting that demonstrates company wide machine vulnerabilities.
All remediation is included in the Global IT MSSP and MSP plans.

Internal Penetration Testing, Reporting